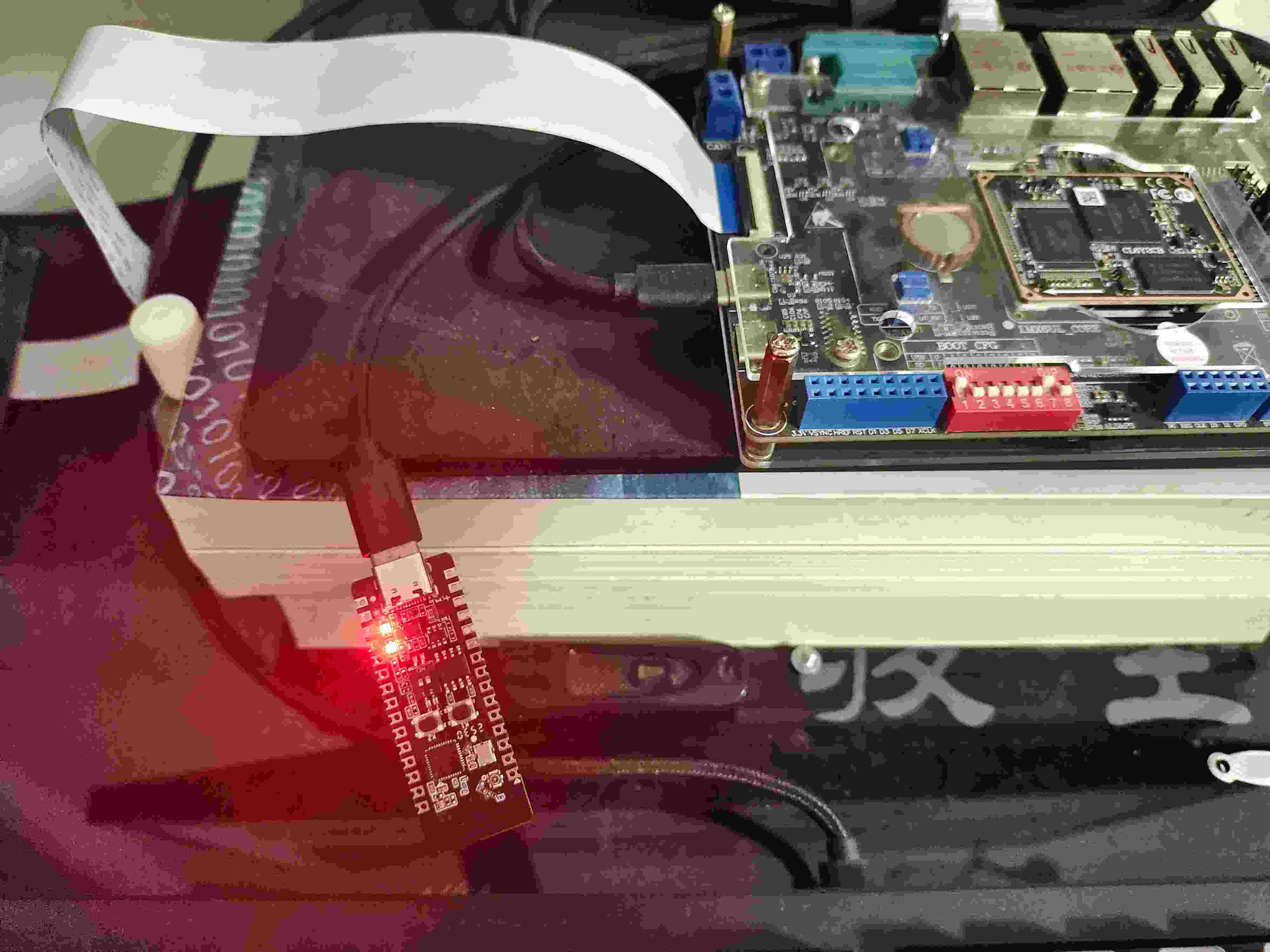
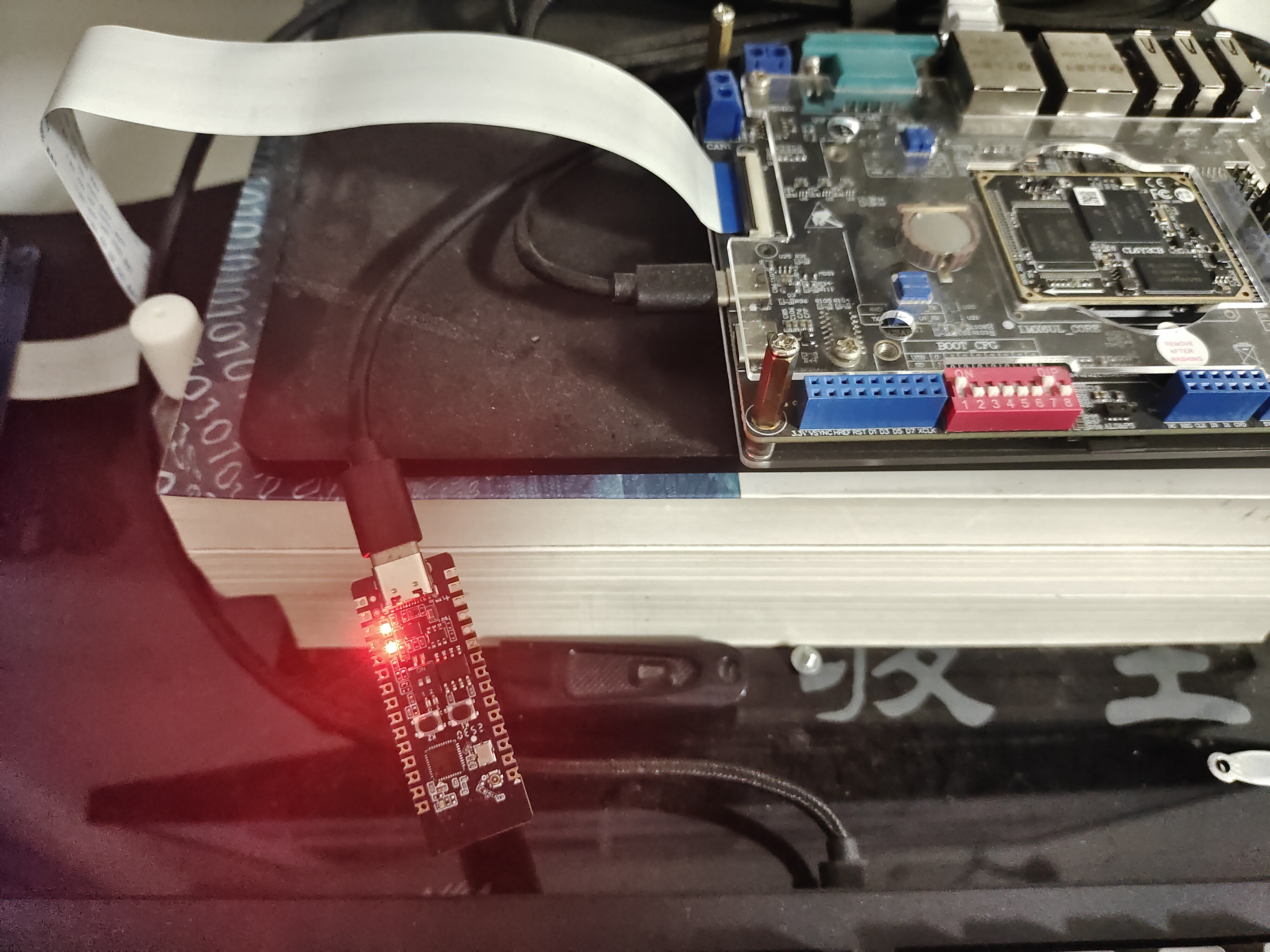
先贴两个上电大图
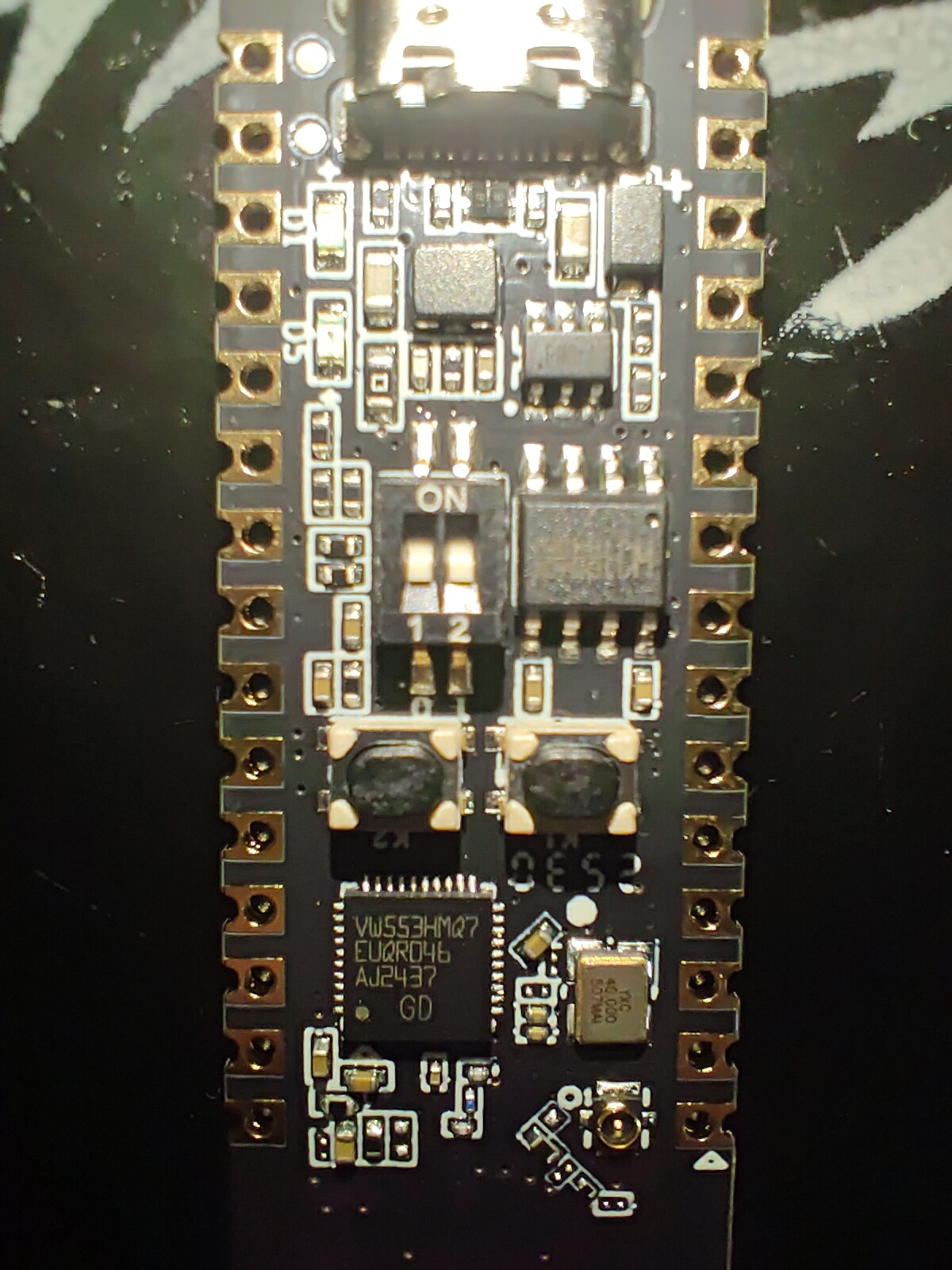
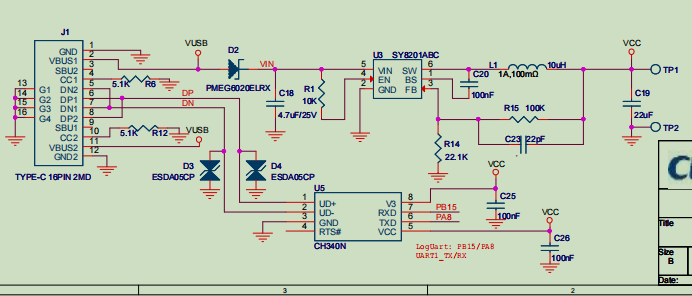
查资料的时候发现V2版和V1版相比,更改了USB的接口电路,相比V1版,V2的USB加上了CH340芯片,可以直接连到UART1。boot的拨码开关boot0(上图的1号)拨到ON就可以切换到bootloader启动,直接通过USB下载程序到flash,无需再使用gd link了,更加方便。
项目的创建和下载其它评测已经写了很多了,不再赘述,直接看CAU模块。
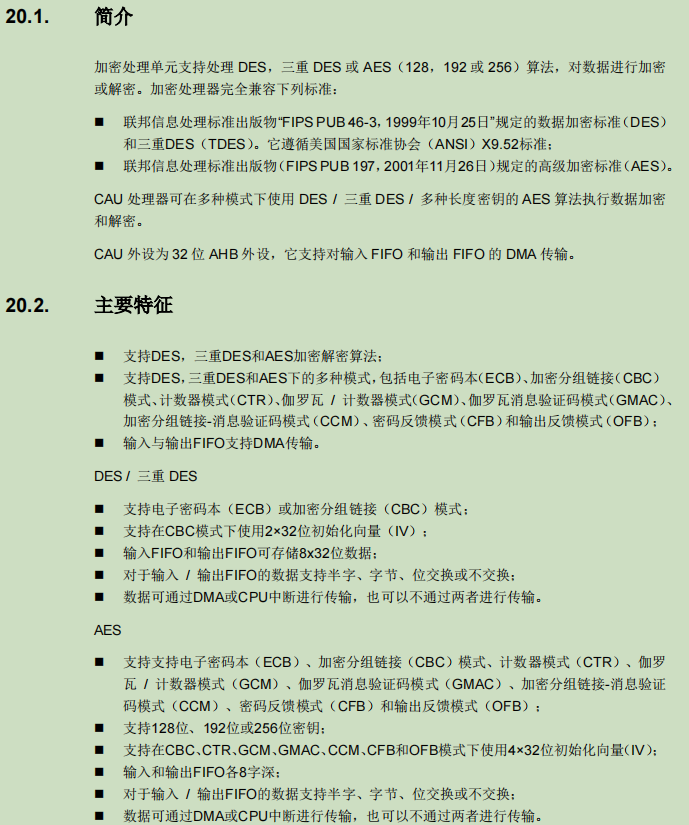
CAU支持的加密模式还是挺多的,咱们就挑常用的AES加密试试水。具体加密流程和使用方式,用户手册的第20章写的很详细,这里直接贴上部分测试代码:
__attribute__((aligned(32)))
const uint8_t plaintext[TEXT_SIZE] = {
0x30, 0x31, 0x32, 0x33, 0x34, 0x35, 0x36, 0x37,
0x38, 0x39, 0x41, 0x42, 0x43, 0x44, 0x45, 0x46,
0x47, 0x48, 0x49, 0x4A, 0x4B, 0x4C, 0x4D, 0x4E,
0x4F, 0x50, 0x51, 0x52, 0x53, 0x54, 0x55, 0x56,
0x57, 0x58, 0x59, 0x5A, 0x61, 0x62, 0x63, 0x64,
0x65, 0x66, 0x67, 0x68, 0x69, 0x6A, 0x6B, 0x6C,
0x6D, 0x6E, 0x6F, 0x70, 0x71, 0x72, 0x73, 0x74,
0x75, 0x76, 0x77, 0x78, 0x79, 0x7A, 0x7A, 0x7A
};//(ASCII)0123456789ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyzzz
__attribute__((aligned(32)))
const uint8_t ciphertext_ecb_128[TEXT_SIZE] = {
0xFB, 0xA1, 0x6E, 0x97, 0x43, 0x27, 0x33, 0x25,
0x0B, 0x9E, 0xCB, 0xC3, 0x41, 0x65, 0x0C, 0x2B,
0x4C, 0xB0, 0xB4, 0x65, 0x01, 0xC0, 0x3E, 0x60,
0x51, 0x7A, 0x37, 0x5E, 0x1D, 0x27, 0x12, 0x85,
0x45, 0xEF, 0x64, 0x99, 0xB6, 0x32, 0x75, 0xCB,
0xC6, 0x0E, 0xCE, 0x8B, 0xCD, 0x69, 0xA9, 0x9A,
0x26, 0xBE, 0x34, 0xCA, 0xE9, 0x64, 0xDD, 0x8D,
0x6D, 0x5B, 0x21, 0xD7, 0x51, 0xE9, 0xB0, 0xA4
};
__attribute__((aligned(32)))
const uint8_t ciphertext_ecb_192[TEXT_SIZE] = {
0x05, 0xEA, 0x91, 0x83, 0x3B, 0x5F, 0xC0, 0x3B,
0xA2, 0xE6, 0x47, 0x24, 0x68, 0xF2, 0x80, 0xE7,
0x8B, 0x04, 0x89, 0xB2, 0x30, 0x66, 0xB4, 0xAD,
0x45, 0x52, 0xF4, 0x0F, 0x11, 0x00, 0xFD, 0x5B,
0x36, 0x44, 0xD5, 0x2A, 0x57, 0xBA, 0x14, 0x68,
0xAA, 0x9F, 0x93, 0xDE, 0xAE, 0x3D, 0x23, 0x9E,
0x62, 0x8A, 0xC6, 0xFC, 0x13, 0x1B, 0xAA, 0xA3,
0x5D, 0x01, 0x52, 0xC5, 0x2F, 0xF2, 0xA0, 0x23
};
__attribute__((aligned(32)))
const uint8_t ciphertext_ecb_256[TEXT_SIZE] = {
0xF5, 0xA0, 0xDC, 0xAA, 0x55, 0x26, 0x8F, 0x6F,
0xD9, 0x8A, 0x30, 0x30, 0xFC, 0xB7, 0xD5, 0xE7,
0xCE, 0xBB, 0xD7, 0xC7, 0x14, 0x67, 0xBC, 0x0C,
0xFA, 0x31, 0xDB, 0x52, 0x5B, 0xC2, 0x2F, 0x34,
0x97, 0x32, 0x73, 0x9C, 0x2C, 0xD8, 0x72, 0x4A,
0x94, 0xCC, 0xF7, 0xA3, 0xD7, 0x0E, 0xDA, 0xB9,
0xE7, 0xB6, 0x1C, 0x01, 0xB0, 0x7E, 0x70, 0x1B,
0xE5, 0x7D, 0xC7, 0x97, 0xBC, 0xBE, 0x7F, 0xA3
};
const uint8_t *ciptxt_ecb_select[3] = {ciphertext_ecb_128, ciphertext_ecb_192, ciphertext_ecb_256};
__attribute__((aligned(32)))
const uint8_t key_128[16] = {
0x61, 0x62, 0x63, 0x64, 0x65, 0x66, 0x67, 0x68,
0x69, 0x6A, 0x6B, 0x6C, 0x6D, 0x6E, 0x6F, 0x70
};//(ASCII)abcdefghijklmnop
__attribute__((aligned(32)))
const uint8_t key_192[24] = {
0x61, 0x62, 0x63, 0x64, 0x65, 0x66, 0x67, 0x68,
0x69, 0x6A, 0x6B, 0x6C, 0x6D, 0x6E, 0x6F, 0x70,
0x71, 0x72, 0x73, 0x74, 0x75, 0x76, 0x77, 0x78
};//(ASCII)abcdefghijklmnoprstuvwx
__attribute__((aligned(32)))
const uint8_t key_256[32] = {
0x61, 0x62, 0x63, 0x64, 0x65, 0x66, 0x67, 0x68,
0x69, 0x6A, 0x6B, 0x6C, 0x6D, 0x6E, 0x6F, 0x70,
0x71, 0x72, 0x73, 0x74, 0x75, 0x76, 0x77, 0x78,
0x79, 0x7A, 0x7A, 0x7A, 0x7A, 0x7A, 0x7A, 0x7A
};//(ASCII)abcdefghijklmnoprstuvwxyzzzzzzz
const uint8_t *key_select[3] = {key_128, key_192, key_256};
uint16_t keysize[3] = {128, 192, 256};
int main(void)
{
cau_parameter_struct text;
uint8_t *key_addr;
uint32_t key_size;
gd_eval_com_init(EVAL_COM0);
/* enable CAU clock */
rcu_periph_clock_enable(RCU_CAU);
gd_eval_led_init(LED1);
printf("\r\nplain text :\r\n");
data_display(TEXT_SIZE, (uint8_t *)plaintext);
/* 初始化 CAU */
cau_deinit();
cau_struct_para_init(&text);
/* 在 ECB 模式分别进行128/192/256三种长度的加解密测试 */
/* ECB mode: AES 128 -> AES 192 -> AES 256 */
for(i = 0; i < 3; i++) {
key_addr = (uint8_t *)key_select[i];
key_size = keysize[i];
text.alg_dir = CAU_ENCRYPT;
text.key = key_addr;
text.key_size = key_size;
text.input = (uint8_t *)plaintext;
text.in_length = TEXT_SIZE;
if(SUCCESS == cau_aes_ecb(&text, encrypt_result)) {
printf(" \r\n\r\nEncrypted Data with AES %d Mode ECB :\r\n", key_size);
data_display(TEXT_SIZE, encrypt_result);
data_check((uint8_t *)&encrypt_result[0], (uint8_t *)(ciptxt_ecb_select[i]), TEXT_SIZE);
}
key_addr = (uint8_t *)key_select[i];
key_size = keysize[i];
text.alg_dir = CAU_DECRYPT;
text.key = key_addr;
text.key_size = key_size;
text.input = encrypt_result;
text.in_length = TEXT_SIZE;
if(SUCCESS == cau_aes_ecb(&text, decrypt_result)) {
printf(" \r\n\r\nDecrypted Data with AES %d Mode ECB :\r\n", key_size);
data_display(TEXT_SIZE, decrypt_result);
data_check((uint8_t *)&decrypt_result[0], (uint8_t *)&plaintext[0], TEXT_SIZE);
}
}
}最后的执行结果如下:
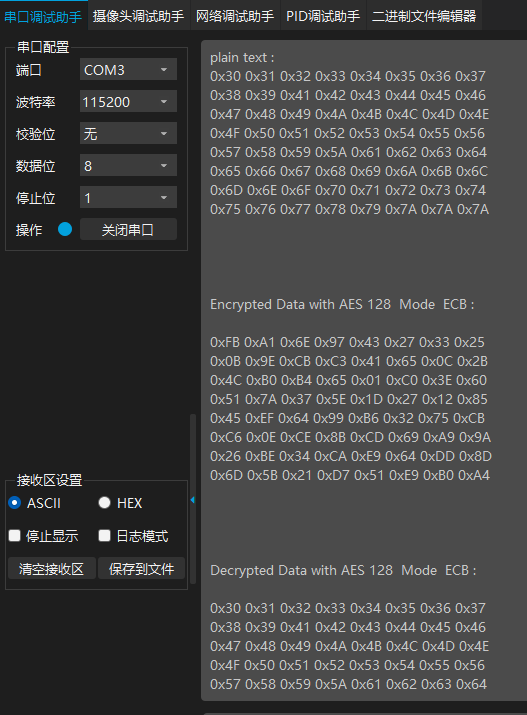
硬件模块实现的加解密算法要比软件实现的算法速度快许多,在需要加密传输的场景下即节省cpu时间,又节省了flash空间。

 开源社区
开源社区